- Create the lambda IAM policy
Go back to your AWS Cloud9 terminal as you will update the AWS Lambda created execution role using the AWS CLI
You will first create a new IAM policy document with the required permissions and apply that to the role. Before you do that you will need to have the ID of the current AWS region and the name of the S3 bucket previously created. If you don’t remember those you can run the commands below in your AWS Cloud9 terminal.
-
Retrieve the current AWS region ID:
#Install dependencies sudo yum -y install jq export AWS_REGION=$(curl -s http://169.254.169.254/latest/dynamic/instance-identity/document | jq -r .region) -
List your Amazon S3 buckets and pick the one you just created. It should be called serverless-XYZ where XYZ is a random string.
aws s3api list-buckets --query "Buckets[].Name" --output table -
Set the following variable with your S3 bucket name. Remember to replace the <your-s3-bucket-name> with the exact name of your bucket.
export MY_S3_BUCKET=<your-s3-bucket-name> -
Create a new policy text document (lambda-policy) in JSON format with the required permissions for your Lambda function. This policy enables your Lambda function to access AWS Systems Manager (SSM). Copy paste the following
cat > lambda-policy << EOF { "Version": "2012-10-17", "Statement": [{ "Effect": "Allow", "Action": ["ssm:SendCommand"], "Resource": [ "arn:aws:ec2:$AWS_REGION:*:instance/*", "arn:aws:ssm:$AWS_REGION::document/AWS-RunShellScript", "arn:aws:s3:::$MY_S3_BUCKET/ssm"] }, { "Effect": "Allow", "Action": ["ssm:GetCommandInvocation"], "Resource": ["arn:aws:ssm:$AWS_REGION:*:*"] }, { "Effect": "Allow", "Action": ["s3:*"], "Resource": [ "arn:aws:s3:::$MY_S3_BUCKET", "arn:aws:s3:::$MY_S3_BUCKET/*"] }] } EOF -
Create the IAM policy using the following command
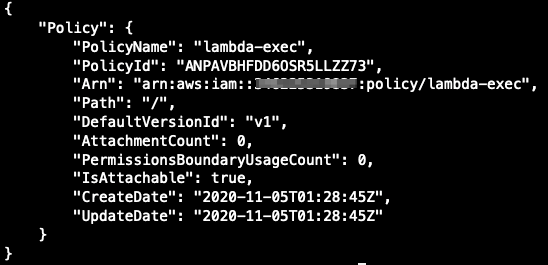
aws iam create-policy --policy-name lambda-exec --policy-document file://lambda-policy -
You should see an ouput as below
-
Now you have created a new IAM policy (policy name lambda-exec) with the necessary permissions for your Lambda function. Next, we will apply this policy to the Lambda created execution role